
Govern AI everywhere
Apply unified governance across analytics, models, and agents inside the platform and beyond it. Maintain visibility, control cost, and mitigate risk at enterprise scale.

Enterprise governance for every AI initiative
Enforce governance from data to decision with one unified framework for visibility, control, and compliance across every AI workload.
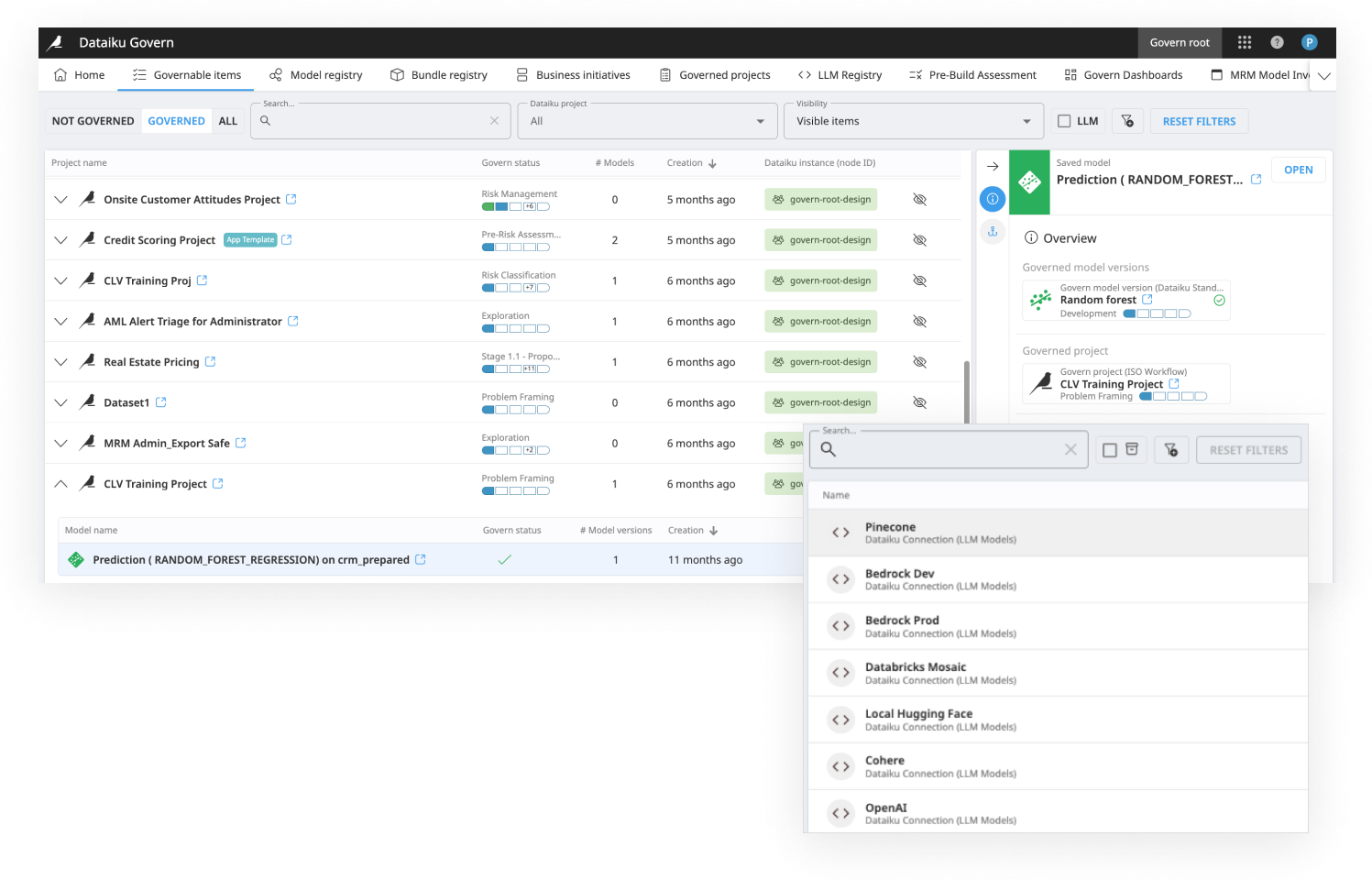
Centralize oversight across all AI
Establish a single system of record for AI initiatives from traditional analytics to generative AI and agents so nothing operates without visibility or accountability.
Unified AI inventory
Track datasets, analytics, models, and agents in one centralized registry with clear ownership, status, and metadata across teams and environments.
Standardized governance workflows
Enforce approval processes, policy checks, and sign-offs aligned to your governance standards blocking deployment until requirements are met.
Dataiku Agent Management
Ensure agents deliver real business value by tracking performance, detecting drift, and maintaining governance at scale.
Transparency and explainability built in
Governance isn’t an afterthought. Lineage, explainability, and documentation are embedded directly into how AI is built and operated.
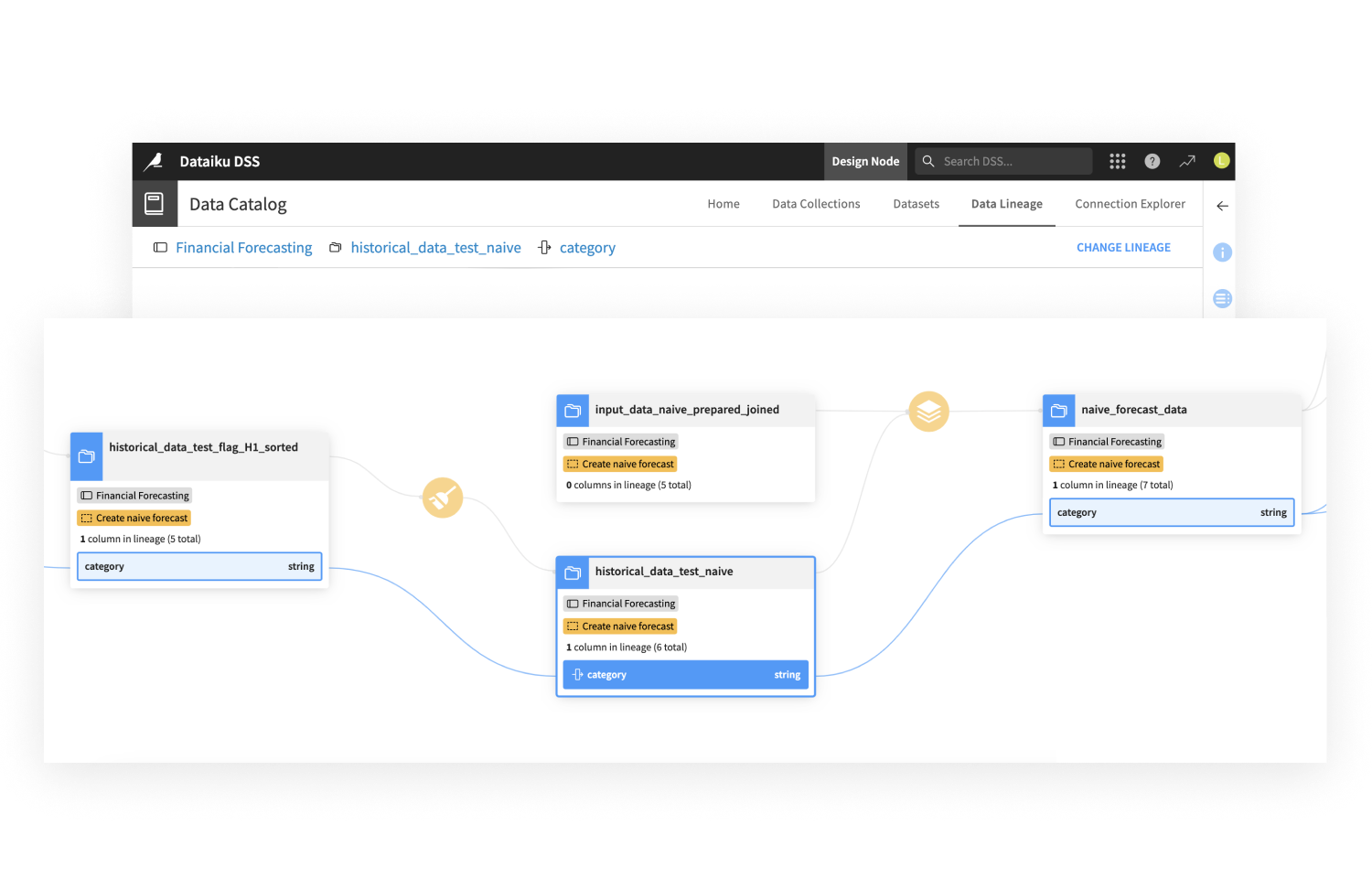
End-to-end lineage
Trace how data, features, models, and agents connect providing full visibility into how insights and decisions are produced.
Explainable AI outcomes
Give technical and business users clarity into model behavior, feature influence, and agent decisions supporting trust and accountability.
Automated documentation
Generate and maintain reusable documentation that captures logic, assumptions, and changes making AI decisions easier to understand and defend.
Reduce risk with continuous controls
Manage risk across the AI lifecycle from experimentation to production without slowing teams down.
Continuous quality and bias monitoring
Detect drift, bias, and performance degradation before and after deployment keeping AI outcomes reliable over time.
Secure and compliant usage
Apply guardrails for sensitive data and generative AI workflows, enforcing safe usage and compliance across teams and tools.
Govern data and AI together
Unify data access controls, cataloging, and AI governance to create a consistent foundation of trust across the enterprise.
Ready for AI success?