This DSS plugin completes your SSO setting by offering some degree of synchronization between selected groups of Azure Active Directory users and the DSS user list.
Plugin information
| Version | 1.0.5 |
|---|---|
| Author | Dataiku |
| Released | 2020-11-06 |
| Last updated | 2021-08-12 |
| License | Apache Software License |
| Source code | Github |
| Reporting issues | Github |
How to set up
- From the Azure Portal, go to Azure Active Directory > App registrations create a new App (New registration).
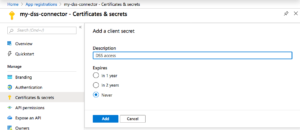
- Click on the newly created app. Copy the Application ID. Then go to the Certificates & secrets > New client secret tab. Set a description, choose an expire date, and copy the value of the created secret.
Add a client secret to the app - Then navigate to the API permissions > Microsoft Graphs > Application permissions and add the following permissions: Group.Read.All and User.Read.All. Finally, grant admin consent for these permissions.
The API permissions tab should appear as above - Find you tenant ID by navigating to Azure Portal > Azure AD > Manage > Properties
- Once the plugin is installed, go to App > Plugins > Installed > Azure Active Directory Sync > Settings.
- Create an authentication preset using the Application ID, Secret ID and tenant ID.
How to use
- In a DSS project, create a table containing the following columns:
- dss_group_name
- aad_group_name,
- dss_profile
- For each row, give the name of the group on AAD, its equivalent group name on DSS, and the user profile you which to associate to this group. The profile can take the following values: DATA_SCIENTIST, DATA_ANALYST, EXPLORER or READER
- A second dataset can be created for logging purpose. This dataset should contain the following columns
- date
- user
- type
- message
- In the DSS project containing the group dataset, go to the macro menu and select Synchronize Azure AD Users with DSS. Select the Azure AD connection created in step 2 of the set up phase, and point Group dataset and Save logging into toward the correct datasets.
- First make sure Simulate is selected, and press Run Macro. A list of the operation to be performed should appear.
- Once you are happy with the synchronization operation to be performed, unselect Simulate and run the macro.
Limitations
Please note that:
- Users created on the DSS side will have DSS handles based on their Azure Active Directory email address, with @ and # being replaced by an underscore character. For instance,
[email protected]will havejohn.doe_mycorp.comhandle on DSS. - Local users already created on DSS will be untouched by the synchronization
- Any change on users performed on the DSS side will not be reflected on Azure AD. The AD remains the source of truth for synchronized users.